Trigona was a double extortion ransomware group discovered in October 2022 and active until October 2023, when the Ukrainian hacktivist group Ukrainian Cyber Alliance compromised its entire infrastructure — affiliate panel, victim database, negotiation server and source code — putting an end to it. It published more than 100 victims on its DLS, although the real number is significantly higher.
It operated under a RaaS model, with different affiliates using the same locker. Its most characteristic trait was a methodical and patient modus operandi: attackers would remain in the network for weeks before detonating the ransomware, consolidating access and quietly exfiltrating data.
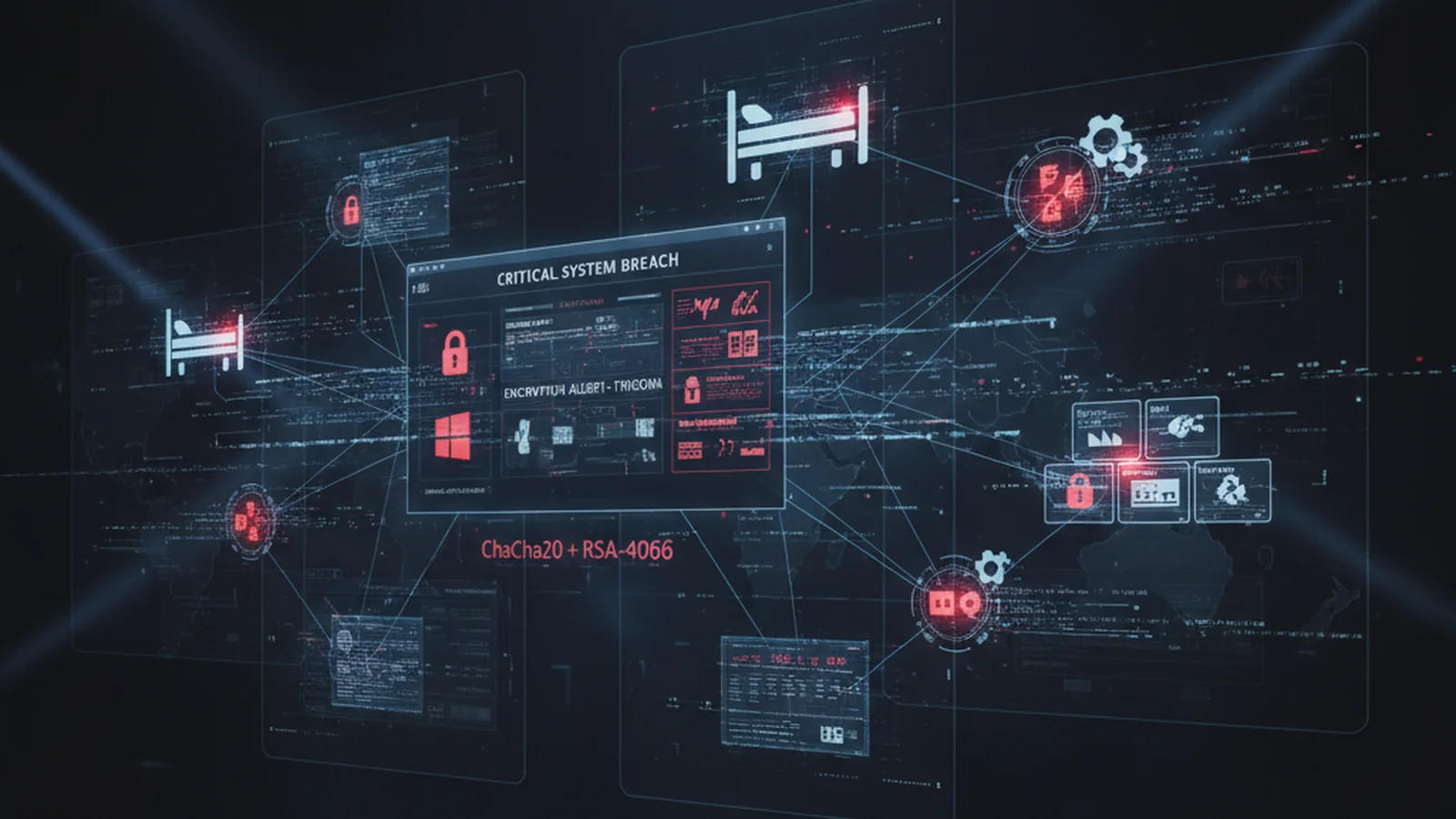
Attack Summary
| Phase | Description |
|---|---|
| Initial Access | RDWeb/RDP credentials purchased from IABs or via credential stuffing (no MFA) |
| Reconnaissance | NetScan to map hosts with open RDP/SMB, network share discovery |
| Credential Access | WDigest (zam.bat) + Mimikatz in memory → Domain Admin within hours |
| Lateral Movement | SMB with DA credentials, propagation to SQL Server, backups and NAS |
| Exfiltration | Rclone against SQL databases and file servers before encryption |
| Persistence | sys account hidden via SpecialAccounts\UserList, auto-start services |
| Anti-recovery | coba.bat — Shadow Copy deletion + Windows Defender deactivation |
| Impact | ChaCha20 + RSA-4096 on Windows; ESXi locker for .vmdk/.vmsn |
Initial Access
The most frequently documented vector is the purchase of valid credentials from Initial Access Brokers (IABs) to access RDWeb or RDP services exposed without MFA. Alternative: credential stuffing with data from previous breaches. Without MFA, access was immediate and required no technical exploitation.
Credential Access
Once inside, Trigona executed its own script called zam.bat which enabled WDigest in the registry (UseLogonCredential=1) to force credentials to be stored in plaintext in LSASS. It then executed Mimikatz in memory to extract them. With Domain Admin credentials, full escalation was typically completed within hours.
️ Persistence and Evasion
Creation of local sys user and addition to the Administrators group
Hiding of sys user via registry key SpecialAccounts\UserList = 0 — invisible on login screen
References to administrators SID (S-1-5-32-544) in PowerShell to evade detection by group name
SQL Server as pivot: execution of reconnaissance tools and backdoors from sqlservr.exe
Exfiltration
Before encrypting, Trigona exfiltrated complete SQL databases and file server content via Rclone to cloud storage controlled by the attacker. This prior exfiltration was the foundation of double extortion: pay to decrypt the data AND to prevent publication.
Impact and Destruction
The coba.bat script handled pre-encryption destruction:
Shadow Copy deletion with vssadmin, wmic and bcdedit
Disabling Windows Defender
Destruction of backups accessible via SMB
The Windows locker uses ChaCha20 + RSA-4096. The ESXi locker directly encrypted .vmdk and .vmsn files in /vmfs from the hypervisor — a single execution left the entire virtualised infrastructure inoperative.
End of Trigona
In October 2023, Ukrainian Cyber Alliance penetrated Trigona’s servers and defaced the affiliate panel. They published screenshots of the source code, victim database and negotiation conversations — and deleted the rest. Trigona’s operations never recovered. Its codebase, however, continued in the hands of other groups: BlackNevas is the most active derivative at the time of publication.
Sources
- The DFIR Report — Trigona Ransomware in 3 Hours
- The DFIR Report — From OneNote to RansomNote
- SentinelOne Anthology — Trigona
- Ukrainian Cyber Alliance — Takedown Statement
Target Sectors
Sectors in which the Trigona group has concentrated its attacks.
Trigona actively targeted industrial and manufacturing companies, taking advantage of the prevalence of unpatched legacy Windows systems and poor network segmentation between OT and IT.
Healthcare organisations were a priority target due to their low tolerance for downtime and the sensitivity of patient data, which increased the likelihood of ransom payment.
Financial and insurance entities were attacked for the value of their databases and the regulatory pressure that forces them to restore operations quickly.
Mid-sized companies with RDWeb or RDP services exposed to the internet without MFA were the most exploited entry vector. The lack of internal segmentation facilitated subsequent lateral movement.
Detection & Response Rules
Rules ready to import into SentinelOne XDR. Contact us for full access to the updated repository.
Detects suspicious child processes launched from sqlservr.exe. Trigona used SQL Server as a pivot to execute reconnaissance tools and backdoors.
event.type = "Process Creation"
AND src.process.name = "sqlservr.exe"
AND tgt.process.name in ("cmd.exe", "powershell.exe", "pwsh.exe", "wscript.exe", "cscript.exe", "mshta.exe", "certutil.exe", "regsvr32.exe", "rundll32.exe", "bitsadmin.exe", "curl.exe", "wget.exe")Detects hiding of user accounts via SpecialAccounts\UserList. Trigona hid the sys user created during lateral movement.
event.type = "Process Creation"
AND tgt.process.image.path endswith '\\reg.exe'
AND tgt.process.cmdline contains '\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\Winlogon\\SpecialAccounts\\UserList'
AND tgt.process.cmdline contains 'add'
AND tgt.process.cmdline contains '/v'
AND tgt.process.cmdline contains '/d 0'Variant executed via reg.exe or PowerShell. Detects writing to SpecialAccounts\UserList from the command line.
event.type = "Process Creation"
AND tgt.process.cmdline contains '\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\Winlogon\\SpecialAccounts\\UserList'
AND tgt.process.cmdline contains 'add'
AND tgt.process.cmdline contains '/v'
AND tgt.process.cmdline contains '/d 0'Detects references to the local Administrators group SID in PowerShell. Trigona used this to obfuscate the addition of administrator users.
event.type = "Command Script"
AND src.process.cmdline contains 'S-1-5-32-544'Detects execution of NetScan (SoftPerfect) and Nmap on the endpoint. Trigona used NetScan to map hosts with open RDP/SMB ports before spreading laterally via PSEXEC/PAEXEC.
event.type = "Process Creation"
AND (
tgt.process.name in ("netscan.exe", "nmap.exe")
OR tgt.process.publisher contains:anycase "SoftPerfect Pty. Ltd."
OR tgt.process.publisher contains:anycase "Nmap Software LLC"
)Detects the creation on disk of a file containing 'netscan' in its path. Attackers typically download NetScan to temporary or user paths before executing it.
event.type = "File Creation"
AND tgt.file.path contains:anycase "netscan"Detects NetScan artefacts (delete.me) on network shares. Trigona used NetScan to discover hosts with RDP/SMB before spreading laterally.
Detects execution of AnyDesk. Trigona and affiliated groups used legitimate remote access tools to maintain persistence and an alternative C2 channel during intrusions.
event.type = "Process Creation"
AND (tgt.process.name in ("AnyDesk.exe", "AnyDeskMSI.exe")
OR tgt.process.publisher contains:anycase "AnyDesk Software GmbH"
OR src.process.publisher contains:anycase "AnyDesk Software GmbH")Detects installation or execution of Atera RMM agent. Attackers install Atera as a persistent backdoor to maintain remote access even if other payloads are removed.
event.type = "Process Creation"
AND (tgt.process.publisher contains:anycase "Atera Networks Ltd"
OR src.process.publisher contains:anycase "Atera Networks Ltd"
OR tgt.process.name = "AteraAgent.exe"
OR (tgt.process.name = "msiexec.exe"
AND tgt.process.cmdline contains:anycase "AteraAgent"))Detects Shadow Copy deletion with vssadmin/wmic/bcdedit. Exact pattern of the coba.bat script documented in Trigona attacks.
event.type = "Process Creation"
AND (
(tgt.process.name = "vssadmin.exe" AND tgt.process.cmdline contains:anycase "delete shadows")
OR (tgt.process.name = "wbadmin.exe" AND tgt.process.cmdline contains:anycase "delete")
OR (tgt.process.name = "bcdedit.exe" AND tgt.process.cmdline contains:anycase "recoveryenabled no")
OR (tgt.process.name = "wmic.exe" AND tgt.process.cmdline contains:anycase "shadowcopy delete")
)Detects enabling of WDigest to store credentials cached in LSASS. Trigona enabled WDigest via zam.bat before running Mimikatz.
event.type in ("Registry Value Create", "Registry Value Modified")
AND registry.keyPath contains "SecurityProviders\\WDigest"
AND registry.valueName = "UseLogonCredential"
AND registry.value = "1"